The Wake of the Solar Hurricane
On Dec 13 SolarWinds, vendors of incredibly commonplace network monitoring tools, published a security advisory noting that their Orion platform had been compromised, leaving nearly 18000 customers - including numerous government agencies - compromised and vulnerable.

On Dec 13 SolarWinds, vendors of incredibly commonplace network monitoring tools, published a security advisory noting that their Orion platform had been compromised, leaving nearly 18000 customers - including numerous government agencies - compromised and vulnerable.

The attack was discovered by FireEye researchers, who were investigating an attack disclosed earlier this month which resulted in the exfiltration of a number of offensive tools used by the company.
The exploit, dubbed 'SUNBURST' by the FireEye researchers, comes in the form of a trojan, compromising a dll file with malicious code. The tainted dll file then communicates with a remote server, controlled by the attackers, via HTTP and obfuscates the nature of the network traffic.

It is believed the exploit has been used since March 2020, with the US Cybersecurity and Infrastructure Security Agency attributing it to an APT group on December 17. Noting the “demonstrated patience, operational security, and complex tradecraft” of the actor, CISA further suggests victims of the attack be 'highly conscious of operational security' when investigating and remediating the hack.
Since publicly announcing the attack, Microsoft, FireEye and GoDaddy collaborated to take control of a domain used in the attack, 'avsvmcloud[.]com'. Since this announcement, researchers at FireEye have been able to use the domain as a killswitch. Taking advantage of how the malware behaves depending on the response from this domain, its hoped the current form of SUNBURST will no longer be functional.

However, this breakthrough does not revoke access the APT may have pivoted to inside of previously compromised systems.
Information on this attack is moving fast - with the majority of effort now focused on determining if the APT were in-fact able to pivot once Command and Control of Orion installs had been established. Noted in their thorough examination, FireEye discovered the use of 'TEARDROP', a bespoke dropper, used to deploy the infamous Cobalt Strike BEACON tool. Given the level of sophistication demonstrated by the APT and the length of time this exploit has been in the wild, the odds of this supply-chain hack being used to pivot further horizontally and vertically across networks is high. This is especially unsettling given the omnipresence Orion holds with US Federal Agencies, Fortune 500 companies, education, tech, communications and more.
Ultimately the actor behind this attack is yet to be officially determined, although some suggest Russian involvement.

By Numbers Sources
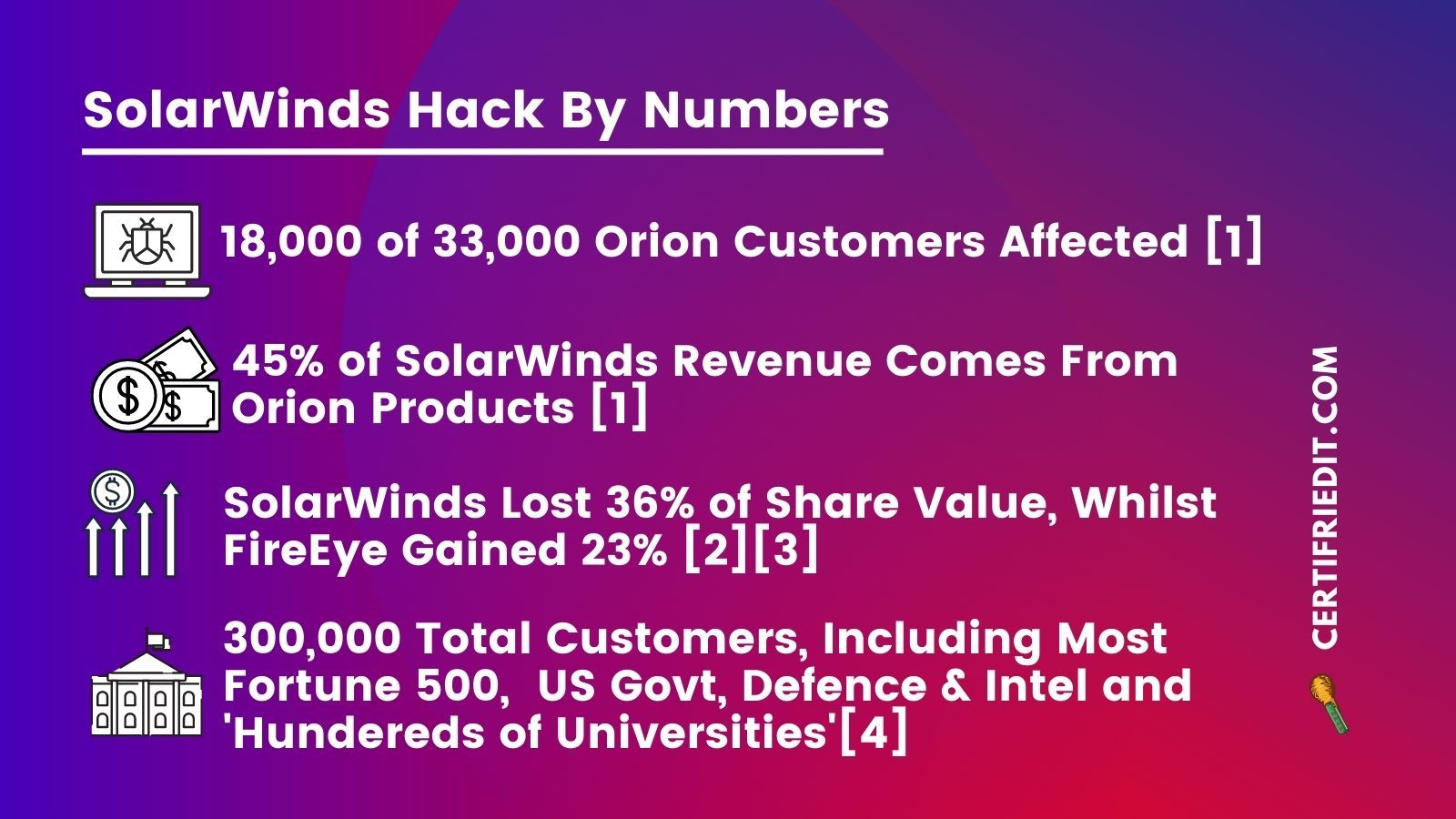
18000 affected of 33000 Orion customers [1]
45% of SolarWinds revenue comes from Orion products, $343 mm [1]
Lost 36% of share value, whilst FireEye rose 23% [2][3]
300,000 total customers, including most Fortune 500 companies, US Government, Defence and Intelligence agencies and ‘hundreds’ of universities. [4]
